CRA Government Affairs releases 2003 Issues Agenda
CRA Committee on Government Affairs
ISSUES AGENDA
February 2003
IT R&D Funding in the FY 2004 Budget Cycle
Federal funding for information technology research and development is a $2 billion effort across seven major agencies, coordinated under the Networking and Information Technology R&D (NITRD) program. The chart below shows the funding history of the program from FY 00 through the President�s FY 04 budget request.
NETWORKING AND IT R&D PROGRAM
(in millions) |
| Agency | FY 00 Actual | FY 01
Actual | FY 02
Estimate | FY 03
Proposed | FY 04
Proposed | Percent Change:
2003 - 2004 |
| NSF | 496 | 641 | 662 | 678 | 724 | 6.8 |
| Defense | 285 | 349 | 439 | 442 | 461 | 4.3 |
HHS | 214 | 244 | 347 | 374 | 441 | 17.9 |
| Energy | 331 | 475 | 306 | 310 | 317 | 2.3 |
| NASA | 129 | 177 | 181 | 213 | 195 | -8.5 |
| Commerce | 36 | 39 | 36 | 38 | 39 | 2.6 |
| EPA | 4 | 4 | 2 | 2 | 2 | 0.0 |
| DHS | ? |
| Total | 1495 | 1929 | 1973 | 2057 | 2179 | 5.9 |
Though the numbers look somewhat encouraging - a 5.9 percent proposed increase in NITRD programs is twice the level of increase the President requested in his FY 03 budget - they are misleading. Because Congress has still not concluded work on 11 of the 13 annual appropriations bills necessary to fund government activities in FY 2003, the President's budget uses the funding levels he proposed in his FY 03 request as the baseline for comparison. The final numbers approved by Congress for FY 03 are likely to be significantly higher than the President's original request � so much so, in fact, that many of the 'increases' the President proposes for FY 04 will actually appear to be decreases in funding over the final FY 03 level.
For example, the President proposes $724 million in NITRD funding at NSF, $584 million of that in NSF's Computer and Information Science and Engineering directorate, an increase of 10.9 percent for CISE over the Administration's FY 03 plan. However, both the House and Senate Appropriations Committees approved increases of more than 15 percent for CISE, and the Senate version of the final Omnibus bill includes an increase of 15.8 percent to the CISE budget ($596.15 million total). When compared to these likely final numbers, the President's proposed budget of $584 million appears to be a $12 million cut to NSF CISE.
Another factor that makes the Administration's proposal for NITRD funding in FY 04 difficult to interpret is the absence of detail concerning the new Department of Homeland Security's Science and Technology directorate and Homeland Security Advanced Research Projects Agency. The President proposes $803 million in funding for the new directorate, but it is not clear what, if any, portion of that funding will go towards NITRD-related research.
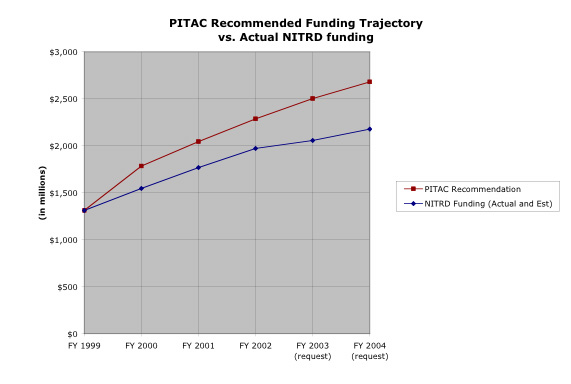
Though it is clear that information technology remains a high-priority for research in this Administration - NITRD in one of only three 'select' interagency initiatives (National Nanotechnology Initiative and the Climate Change Science Program are the others) - the funding level requested still falls well short of the level recommended by the President's Information Technology Advisory Committee (PITAC). In 1999, PITAC, tasked with reviewing the federal government's IT R&D effort, concluded that federal support for IT R&D was inadequate and too focused on near-term problems; long-term fundamental IT research was not sufficiently supported relative to the importance of IT to the United States' economic, health, scientific and other aspirations; critical problems in computing were going unsolved; and the rate of introduction of new ideas was dangerously low. Included in the report was a series of specific funding recommendations for FY's 2000 through 2004 - a total recommended increase of $1.3 billion over five years. The President's request falls $503 million short of the PITAC recommended level for FY 04.
CRA will work to insure that Congress and the Administration remain aware of the crucial role information technology research and development plays in the nation's prosperity, security and the health of its people, and continue to make the case in support of robust IT R&D funding.
Cyber Security Research and Development
In late 2002, Congress passed and the President signed important legislation authorizing nearly $900 million in new cyber security research and development programs and fellowships over the next five years at NSF and the National Institute of Standards and Technology. Additionally, the FY 03 appropriations process and the President's FY 2004 budget will likely yield actual funding for many of these newly authorized programs - not only at NSF and NIST, but also in the Department of Defense and the new Department of Homeland Security. CRA will continue to monitor the development of these new programs and help insure that addressing the long-term neglect of fundamental cyber security research and development, as well as fostering a community of researchers in this area, remain primary goals.
DARPA and University Research
The university research community, especially the computing research community, is concerned about ways in which the current funding regime at DARPA could discourage innovative research and discourage the participation of university-based researchers. DARPA's recent move to a 'milestone' based approach to funded research - where programs are evaluated on a 12 to 18 month cycle with 'go/no go' decisions at each step - encourages the proposing of less-than innovative research and poses considerable logistical challenges to university-based researchers. CRA made this case to House and Senate Armed Services committee members who agreed with the concerns and added language to the Senate Defense Authorization Act of 2003 committee report to that effect:
Many of the technologies that have enabled our current economic prosperity and increased our national security have their roots in university research supported by the DARPA. For example, the Internet, graphical user interfaces, and global positioning systems are all the result of long-term, cutting-edge, university-based research, supported decades ago by DARPA. DARPA has been recognized as the high-risk, high-payoff defense agency ever since its inception. The committee, however, is concerned about recent trends in the agency-sponsored research that appear more shortsighted in their approach, particularly the emphasis on 12- and 18-month reviews in order to attempt to eliminate non-promising technologies.
The committee supports effective internal oversight and commends DARPA for pursuing truly innovative technologies. However, annual reviews may not be appropriate for all basic and applied defense-related research programs. Additionally, these reviews have a discouraging effect on the intended long-term payoff of the research and are especially inconsistent with the time frames and pace of university research. The committee is concerned that this near-term approach to basic and applied research will have detrimental consequences on the ability to develop innovative solutions to future threats. Therefore, the committee urges DARPA to re-evaluate its policies for reviewing and terminating awards in scientific and technical areas where the Department of Defense is dependent on DARPA's ability to do revolutionary research that requires some time to develop and mature.
Additionally, while the integration and application of IT throughout the DARPA's programs has real benefits, CRA members have expressed concern that research aimed at advancing the leading edge of IT has not received adequate focus within the agency. CRA believes the DARPA office most responsible for fundamental IT research, the Information Processing Technology Office (IPTO), should support a broad scope of national-level, urgent topics in IT research where DARPA is not currently engaged. These topics include: multi-agent systems; the fundamentals of security (e.g., 'security through diversity'), fundamental advances in databases, data mining, and knowledge discovery; and new approaches to networking.
CRA will continue to work with Members of Congress, the Administration, and the leadership at DARPA to resolve these issues.
DARPA and Total Information Awareness
DARPA's 'Total Information Awareness' research program has been the focus of much criticism and concern. The program, an attempt to 'design a prototype network that integrates innovative information technologies for detecting and preempting foreign terrorist activities against Americans,' has come under fire by many who see the eventual development of such a network as a serious threat to American civil liberties and security. A TIA system, critics say, would be ripe for misuse by authorized users, would be prone to false positives (in which innocent individuals might be identified as candidate terrorists), would pose additional security problems, and, ultimately, would not help the nation protect itself from terrorism.
As an association of computing researchers, CRA shares many of the concerns of TIA's critics. However, CRA believes that research into the development of a system that could address all of those concerns is worthwhile. The technologies that would be required to build a workable version of TIA - information fusion, improved privacy technologies, machine-learning algorithms for data mining - are technologies that have been identified by many, including the National Research Council as worthy of further study. The problems that need solving are, indeed, sufficiently hard ('DARPA-hard') as to be worth the time and investment. Even if the full system as envisioned is not deployable, some components of the system may be effective in anti-terrorism activities.
Therefore, CRA supports continued research in this area and would oppose a moratorium on research similar to that included in recent Senate legislation. CRA would strongly object, however, to any consideration of using a prototype TIA system in any operational way if the concerns delineated above were not adequately addressed.
Women and Underrepresented Groups in Science
CRA continues to monitor current legislation to look for opportunities to include provisions that encourage the participation of women and underrepresented groups in science. In the 107th Congress, CRA worked with members of the House Science Committee to insure legislation they were preparing would continue to encourage mentoring programs and research experiences for women funded through the National Science Foundation.
Impediments to Research
CRA continues to monitor legislation for provisions that could, intentionally or unintentionally, create impediments to the computing research enterprise. CRA will continue to encourage efforts like Rep. Rick Boucher (D-VA) attempt to broaden the research and 'fair use' exemptions for digital content contained in the Digital Millennium Copyright Act (DMCA). As the DMCA currently stands, researchers who employ reverse-engineering techniques crucial to computer security research could find themselves liable for federal or civil penalties under the DMCA's 'anti-circumvention' provisions.
CRA will also continue monitor efforts to allow content providers safe harbor from anti-tampering and trespass laws in order that they can disrupt or disable certain peer-to-peer filesharing activities. This 'authorized hacking' of peer-to-peer networks could have the two-fold effect of crippling legitimate networks upon which researchers rely and hindering the growth of peer-to-peer software, which has many promising future applications.
Academic Freedom
Recent proposals internally in the Department of Defense and recent statements by members of the current Administration have increased the concern among researchers that new restrictions on research deemed 'sensitive' but not classified may be forthcoming. CRA supports the federal government's long-held position that fundamental research (basic research) should remain free of pre-publication review, free from restrictions on personnel, and remain unclassified. Research that is not basic, but not classified, should also remain free of restriction.
CRA will work with our affiliate societies and with other members of the scientific community who are working to craft a broad position in support of academic freedom.
|
|